Advertisements
Advertisements
Customer Analytics firm needs to design a survey form as shown below:
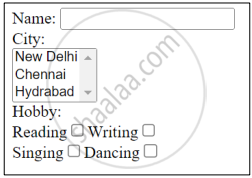
Write suitable HTML code to design it.
Concept: HTML Forms
______ refers to the gap between those who have access to technology and those who do not.
Concept: The Digital Divide
Write any two differences between proprietary and open-source software.
Concept: Open Source Software Movement
Name any 2 issues related to privacy in e-commerce.
Concept: E-Commerce Technology
"Plagiarism is a major problem in the world nowadays". What do mean by plagiarism?
Concept: Plagiarism Property Rights
|
Parminder recently celebrated his 14th birthday. On his birthday he got to know about Facebook. He learned how social networking sites help people to meet their friends and discuss things online. He also found out that he is now eligible to open a Facebook account. He creates his profile on Facebook and starts connecting with his friends. Within a few days, he befriends many people he knows and many people he does not know. After some time he starts getting negative comments on his posts. He also finds that his pictures are being shared online on objectionable websites. |
Based on the given information, answer the questions given below.
- Identify the type of cybercrime Parminder is a victim of.
- After hearing about his ordeal, the school decides to publish a set of moral principles that determines the appropriate behavior of students while using the internet. The school is referring to ______.
- Write a safety measure to be taken by Parminder to avoid threats from unknown people in the future.
- Parminder decides to make a list of common safety precautions to be taken when online. Write any two points that Parminder should include in his list.
- Why are privacy settings so important in social networking sites?
Concept: Netiquettes
Suhani asks her colleague for her project work and then copies the entire work and submits it to her team leader claiming it to be her own work. The act performed by Suhani is known as ______.
Concept: Plagiarism Property Rights
Write the names of any two licensed software.
Concept: Software Licensing
How do Intellectual Property Rights provide protection to digital work?
Concept: Intellectual Property Right
A software ______ is a legal instrument governing the use or redistribution of software.
Concept: Software Licensing
Which software are termed as open-source software?
Concept: Public Access and Open Source Software
Name any two open-source software.
Concept: Public Access and Open Source Software
It is an era of the Internet and we as a netizen spend most of our time in the cyber world. Saumya, a class X student, is new to the cyber world. Help her with the following:
- Suggest any two netiquettes, which she should follow in order to become a good netizen.
- As the last day was approaching, so one of her friends has just submitted the science project by copying and pasting from the internet, without even acknowledging the original source. Is this the right act or wrong? Name the term which is being used for this act.
- E-commerce is growing exponentially and so is the risk involved in it. Mention any two common E-commerce frauds in order to make Saumya aware of it.
- Suggest to her any two precautions to be taken while using E-commerce.
Concept: Netiquettes
What do you understand by the term “Digital Divide”?
Concept: The Digital Divide
